Short on time? Read the key takeaways:
- Retailers need to secure their infrastructure and employees accessing it to protect customers' personal information (PII).
- The pandemic has brought new security challenges to remote work, leading retailers to use advanced security solutions to monitor and detect suspicious activities.
- A hybrid cloud strategy is essential for retailers to store company and customer data securely and improve their operations and customer experience.
- Retailers should assume a cyber-attack will occur and make security a business function, considering it as an entire ecosystem, from employees and customers' access to software, applications, and systems.
The nature of work and how we live, how we consume and how we purchase goods and services are constantly changing.
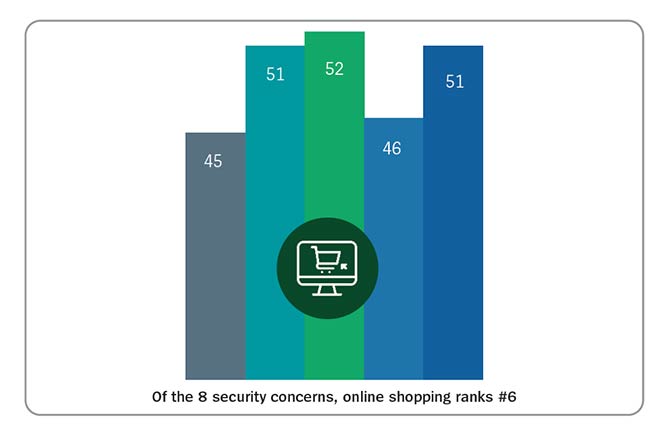
Since the 2021 Unisys Security Index™, there have been several high-profile breaches at well-known retailers. The index further expands on this increased trend, as online shopping security concerns jumped five points — to 51% — compared to last year. Retailers must ensure their clients’ personal identifiable information (PII) integrity. But first, retailers need to secure their infrastructure and the employees accessing it.
Adapt security platforms for remote work
When the pandemic first hit, many companies were unprepared for the security challenges that remote work presents. Gone are the days of using old, non-scalable VPNs. While VPNs have long been a trusted and popular solution for securing remote access to company resources, they are not the best solution to support and secure today’s changing workforce.
Leading retailers are using more advanced security solutions, including fast, encrypted access, identity verification tools and micro-segmentation to limit the damage caused by incoming malware. Advanced security solutions use machine learning to continuously monitor end user and endpoint activities, comparing them to behavior patterns and company policies. This allows security teams to immediately detect unusual activities and identify compromised accounts or insider threats. Providing timely alerts when suspicious activity is identified enables an immediate and highly targeted response. This significantly speeds up incident response and reduces the time attackers have to snoop around your network.
But what about the cloud? It’s impossible to talk about security without considering where you are in your cloud journey.
Source: https://www.unisys.com/unisys-security-index/
Your cloud journey
For retailers, a hybrid cloud strategy is not optional. It’s essential. Imagine storing all company data and customer PII on the same cloud server — all it takes is a single breach, and all your data is exposed. For many, the journey into the cloud is a daunting task. But with the right partner, your move to the cloud can be a seamless transition. You need to think about how your cloud strategy is being defined. Do your risk analysis. Create communities of interest (COIs) and restrict people’s access to only the data they need to access. Today your workforce is remote, and everyone is accessing software, applications, systems and enterprise resource planning (ERP) software remotely. It is imperative that people only have access to the data and systems they need to do their jobs.
Streamline operations
Many brick-and-mortar retailers rely on legacy systems, and these systems are often outdated and disjointed. Legacy systems prevent efficient integration of key business operations, including inventory, shipping, development and point of sale. When retailers move to the cloud, it enables them to deliver seamless customer experiences and allows all departments and locations to have real-time updates on inventory and shipments. With point-of-sale systems moving from cash and credit cards to mobile devices (i.e., smartphones and tablets), retailers can implement cloud solutions for seamless transactions as well as improved customer experiences.
Make shopping personal
Real-time access to customer data, purchasing history, and orders is a game changer for retailers, and cloud computing makes this possible. Moving to the cloud and using analytics empowers retailers to customize offers, promotions and coupons better. Retailers have been sitting on mountains of customer data. Using the cloud and analytics, they can now monetize that data to provide more relevant offers and a better shopping experience for their customers.
Rethink your security
Years ago, when a company was hacked, everything could be unplugged. You would be offline for a couple of weeks, and everything would return to normal. Today, this is impossible. If your disaster recovery plan sits on a shelf gathering dust, you are completely vulnerable to a cyber attack. Your organization must have the ability to recover immediately.
The truth is, no company can consider itself 100% safe, and no vendor can ensure complete protection. The best strategy is to assume a cyber-attack will occur and to map and identify protection solutions for each degree of risk. Today, we see successful organizations looking at security as an entire ecosystem. These organizations are thinking about how employees and customers access software, applications, and systems. Companies that make security a business function are the leaders in their industries.
Conclusion
As demonstrated by the frequency of security breaches, data has become the most valuable commodity of our time. Yet surprisingly, many companies are not even taking basic security measures to comply with this new reality.
No surprise, the future is hybrid cloud for retailers. Hybrid cloud offers maximum flexibility, as retailers have a mix of public and private cloud and on-premises environments. Some may even say public cloud is an evolved sibling of the on-premises environment, except for the shared security responsibility. Those retailers embracing hybrid cloud solutions are the leaders. From streamlining operations to personalization, it’s all about data.
Effectively using customer data to create an exceptional shopping experience is not an option. It’s table stakes. And standing out in a crowded online marketplace is only possible with hyper customization.