Está impossível acompanhar um cenário de negócios em constante mudança? Na Unisys, estamos dando um jeito nisso.
Nós acreditamos que a tecnologia ágil pode inspirar inovações que impulsionam as organizações para o futuro todos os dias. Não importa o setor, trabalhamos em conjunto com clientes em todo o mundo para estimular a inovação no local de trabalho digital, na nuvem, na computação empresarial e em soluções de processo de negócios. Adoramos arregaçar as mangas e colaborar para descobrir soluções que transformam a forma como as pessoas experimentam a tecnologia.
Soluções para romper barreiras
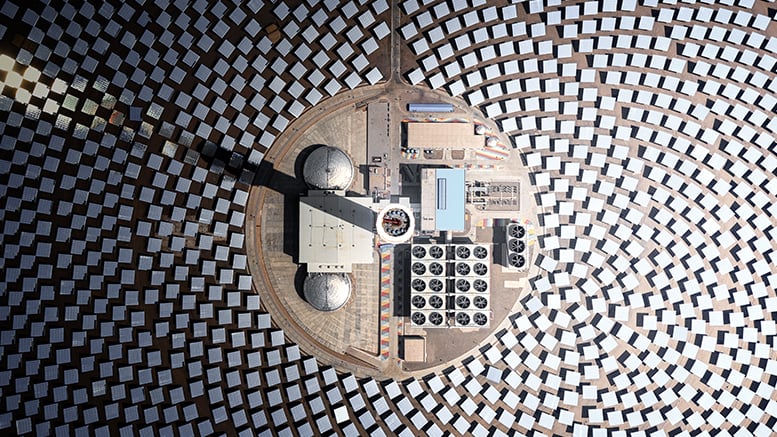
Otimização de logística
Otimize a gestão de logística combinando IA, análises avançadas e computação quântica.
Modernização de aplicações
Eleve seus negócios e envolva os clientes com uma aplicação segura e dimensionável baseada na nuvem.
Inteligência artificial
Saiba como a Unisys pode ajudar sua organização a liberar o potencial ilimitado da IA.
Experiência do funcionário
Crie experiências de funcionários sem atrito, semelhantes às do consumidor, reduzindo custos e aumentando a eficiência.
Resultados dos clientes
Colaborando para maximizar os resultados
Sabemos que avanços desse tipo não acontecem por conta própria. Leva tempo para entendermos os objetivos de nossos clientes e identificarmos soluções que lhes permitam ter sucesso. É quando nos concentramos em um propósito compartilhado para criar algo novo juntos que as coisas se encaixam.
Ver histórias de clientes