Unleash the ultimate
AI use case.
Explore how AI transforms productivity.
ENTERPRISE COMPUTING
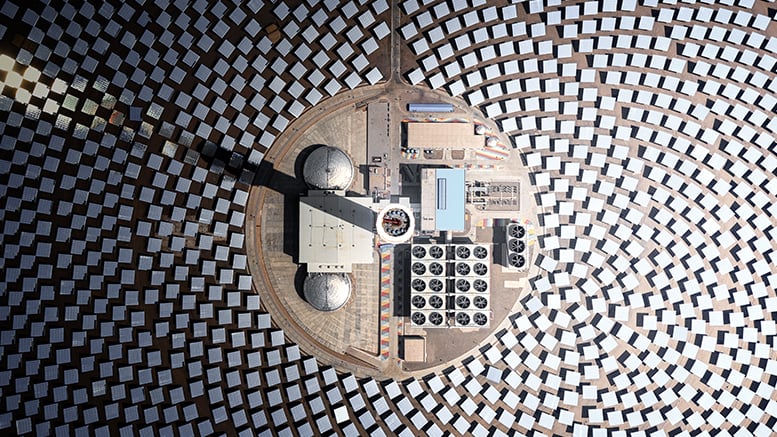
Logistics Optimization
Drive near-real-time decision-making with a quantum computing-powered advanced analytics and artificial intelligence (AI) solution.
Barrier-breaking solutions
Logistics Optimization
Optimize logistics management by blending AI, advanced analytics and quantum computing.
Application Modernization
Elevate your business and engage customers with secure, scalable cloud-based applications.
Artificial Intelligence
Discover how Unisys can help your organization unlock the limitless potential of AI.
Employee Experience
Create frictionless, consumer-like employee experiences while reducing costs and increasing efficiency.
Impossible to keep up with an ever-changing business landscape? At Unisys, we’re pushing back on that.
We believe that agile technology can inspire breakthroughs that propel organizations into the future every day. No matter the industry, we work together with clients around the world to drive innovation through digital workplace, cloud, enterprise computing and business process solutions. We love rolling up our sleeves and collaborating to discover solutions that transform how people experience tech.
Client Outcomes
Collaborating to maximize results
We know that advancement like this doesn’t happen on its own—it happens by taking the time to understand our clients’ goals and pinpointing solutions that enable them to succeed. When we rally around a shared purpose to create something new together, that’s when things click.
View client stories